Over the past several years, I’ve watched digital credentialing shift from decorative certificates to operational infrastructure.
Some of the insights I've curated for this guide come from public data, industry reports, and open standards documentation. Others come from observing how credential programs behave when scaled to greater volumes, where friction surfaces and where systems either hold or don’t.
This piece is not based on feature pages alone. It reflects patterns I’ve seen across institutions, academies, and enterprise programs issuing credentials in meaningful volume.
If you’re evaluating digital credential systems in 2026, my aim is straightforward: to give you a clearer lens before you commit time, budget, or reputation to a system that will likely outlast the current software cycle.
TLDR: Quick Summary
The digital credentialing market is no longer about who can issue a badge. It’s about who can defend it, scale it, and keep it credible five years from now. If you’re evaluating digital credential management tools, here’s what becomes clear quickly:
1.Enterprise organizations still lean toward platforms with employer recognition and established global networks.
2.Academic institutions prioritize audit-ready records and transcript-level credibility.
3.Training providers increasingly care about portability, verification speed, and pricing that does not quietly punish growth.
4.Open standards compliance is no longer niche. Open Badge 3.0 and W3C Verifiable Credentials are steadily entering procurement conversations.
5. And one pattern shows up repeatedly: Tools that merely issue certificates are plateauing. Tools that treat credentials as verifiable infrastructure are separating themselves from mainstream noise.
6.If you’re wondering how that translates into direct ROI, the answer is less dramatic than you expect: It shows up in friction that's been strategically avoided.
7.Before we examine individual platforms, it’s worth understanding what has materially changed over the past year.
What’s Changed Since 2025: The Structural Shifts in 2026
If you read our last year’s comparison of the Top 15 Best Digital Credential Software Tools in 2025, you might reasonably ask what truly changed. At a surface level, many of the same platforms still dominate discussion. The meaningful shifts are more structural than they are cosmetic.
So what you'll see are that several developments distinguish 2026 from 2025's best.
Here are our top contenders:
Open Standards Are Moving From Optional to Expected
Open Badge 3.0 compliance and W3C Verifiable Credentials have moved from niche technical discussions into procurement conversations.
Institutions are no longer asking whether a system can issue digital badges. They are asking whether those credentials are interoperable, wallet-compatible, and portable beyond a single vendor ecosystem.
Portability is increasingly treated as risk mitigation, not technical preference.
This shift affects how digital credential management systems are evaluated. Alignment with open standards now influences long-term platform viability.
Digital Wallet Integration Is Becoming Practical, Not Theoretical
Digital identity wallets are no longer speculative infrastructure.
Public sector initiatives and private identity frameworks are accelerating wallet-based credential presentation. That means credentials must function independently of issuing dashboards.
 In 2025, wallet compatibility was discussed cautiously. In 2026, buyers are beginning to test it.
In 2025, wallet compatibility was discussed cautiously. In 2026, buyers are beginning to test it.
A credential that cannot move into independent wallet environments is increasingly viewed as incomplete.
Verification Expectations Are Rising
Fraud prevention has become a more visible concern.
Static PDF certificates have lost credibility in high-stakes environments. Verification flows are being examined more closely by employers and regulators.
There is growing interest in:
- Tamper-resistant digital certificates
- Independent verification models
- Identity-linked credential issuance
- Anomaly detection and behavioral verification layers
The conversation has shifted from “Does it verify?” to “How defensible is the credential verification process?”
That distinction changes vendor evaluation significantly.
Automation Is Being Evaluated Against Scale, Not Convenience
In 2025, automation was often discussed in terms of operational efficiency.
In 2026, automation is evaluated against projected growth.
Institutions are modeling credential volume increases, multi-program expansion, and cross-border issuance.
API depth, renewal logic, webhook integration, and lifecycle governance are no longer advanced features. They are infrastructure requirements for scaling organizations.
For a deeper look into this topic, read our blog on Scaling Fast: Why Institutions Rely on Digital Credentials for High-Volume Issuance
Search behavior has matured.
Prospective buyers are increasingly searching for:
- Digital credential management systems vs LMS
- Verifiable credentials vs PDF certificates
- Open Badge 3.0 compliant platforms
- Credential lifecycle management software
- Credential portability standards
This reflects a broader shift in understanding.
Credentialing is no longer viewed purely as issuance software. It is increasingly understood as proof infrastructure.
Market Growth Is Accelerating Institutional Interest
Industry projections indicate sustained growth in the digital credential management market over the coming decade.
As adoption increases across higher education, enterprise certification, workforce platforms, and government programs, infrastructure maturity becomes more important than surface functionality.
Early adoption favored experimentation. Current adoption favors durability.
Why This Matters for This Guide
This 2026 comparison is not simply an updated tool list.
It reflects the shift from “Which platform looks best?” to “Which system holds up under scale, migration, verification scrutiny, and standards evolution?”
If you are evaluating digital credential management tools today, you must choose infrastructure over campaign success.
 What Changed for the Digital Credentialing Ecosystem?
What Changed for the Digital Credentialing Ecosystem?
Digital credentials have shifted from convenience artifacts to operational assets.
Several external forces have contributed to this change.
Workforce mobility has increased. Skills-based hiring has become more common. Employers are more likely to request proof of specific competencies rather than rely solely on degrees.
At the same time, credential fraud has become easier. Static PDF certificates can be modified. Screenshots circulate without validation. Verification links sometimes rely on systems that disappear when contracts end.
As a result, organizations are asking more infrastructure-oriented questions:
- Is this credential independently verifiable?
- Is it portable outside our LMS?
- Can it survive vendor migration?
- Does it align with recognized standards?
Open Badge 3.0 and W3C Verifiable Credentials specifications are gaining attention because they address interoperability and portability. Standards reduce long-term risk.
Another shift involves scale.
Issuing 500 credentials per year presents different requirements than issuing 50,000. Manual processes that work at low volume often fail at higher volume. API access, automation logic, and renewal workflows become critical.
Pricing architecture also influences decisions more than before. Some platforms reserve advanced automation or analytics behind higher pricing tiers. That structure may align with enterprise budgets but create friction for growing academies.
 As digital credentials increasingly support workforce mobility, continuing education compliance, and audit defensibility, evaluation criteria have matured.
As digital credentials increasingly support workforce mobility, continuing education compliance, and audit defensibility, evaluation criteria have matured.
The focus has moved from appearance to infrastructure.
The 2026 Buyer Checklist: What Actually Matters in a Credential Management System
Comparing digital credential management tools can quickly turn into feature fatigue. Most platforms demonstrate clean dashboards, smooth issuance flows, and polished verification pages. Those surface impressions are useful, but they rarely expose structural weaknesses.
A more reliable evaluation approach is to test vendors against infrastructure questions rather than interface features.
The checklist below is designed for live demos and procurement conversations. It focuses on durability, scalability, and long-term risk.
1. Verification: Test the Process, Not the Claim
Every vendor claims credentials are “verifiable.” That statement alone is meaningless.
Instead of asking whether verification exists, ask how it works under constraint.
During a demo, request that the vendor walk through the full credential verification process as if you were an employer with no prior context. Measure how long it takes. Observe how many steps are required. Note whether verification requires account login or platform familiarity.
Clarify whether credentials remain verifiable if your subscription ends. Some systems rely entirely on hosted pages within the vendor’s infrastructure. Others provide more durable verification mechanisms.
If verification disappears when a contract lapses, that is not infrastructure. It is hosted convenience.
Also examine how tamper resistance is implemented. Is verification backed by cryptographic proof? Is metadata locked and traceable? Can issuance history be demonstrated clearly?
Verification should be fast, interpretable, and defensible under audit conditions.
2. Portability: Plan for Migration Before You Need It
Portability questions often feel hypothetical during onboarding. They become urgent during migration.
Ask vendors directly whether credentials comply with Open Badge 3.0 specifications or W3C Verifiable Credentials standards. Request documentation rather than summary statements.
Confirm whether learners can export credentials independently. Can they store credentials in external wallets? Are metadata fields structured in machine-readable formats?
Most importantly, ask what happens if your organization migrates systems or changes vendors. Can credential records be exported in standardized formats? Will verification links remain functional?
Portability reduces long-term dependency risk. It also protects learner ownership.
Institutions rarely regret choosing portable infrastructure. They often regret overlooking it.
3. Automation: Identify Scaling Boundaries Early
Automation depth determines how smoothly credential programs expand.
Ask vendors to demonstrate API-based issuance. Clarify whether API access is included at your pricing tier or reserved for enterprise plans.
Confirm whether credentials can be triggered automatically by LMS completions, external system events, or webhook integrations.
Explore renewal and expiration logic. Can credentials update automatically? Can versions be managed without reissuing entirely new records?
At small volumes, manual workflows may seem manageable. At larger volumes, they introduce operational drag and error risk.
Strong credential management systems treat automation as core infrastructure rather than optional enhancement.
4. Analytics: Connect Data to Decisions
Most platforms provide dashboards showing views, shares, and engagement activity.
More relevant analytics examine employer verification behavior, geographic distribution of credential holders, and lifecycle renewal patterns.
Ask whether analytics can be exported into BI systems or compliance reporting frameworks. Determine whether reporting supports audit requirements or regulatory documentation.
If analytics cannot influence program design, renewal strategy, pricing adjustments or employer outreach; they are limited in strategic value.
Data maturity should match the scale and complexity of your credential program.
5. Pricing Architecture: Model Growth, Not Entry
Pricing should be evaluated across projected volume scenarios.
Ask vendors to model cost at current volume, expected growth volume, and high-growth volume. Identify where feature access changes between tiers.
Confirm whether advanced verification, automation, API access, or analytics capabilities are gated behind higher plans.
Clarify whether verification traffic incurs additional cost. Some platforms price per issued credential, others per active credential, and others per user.
Predictable scaling cost enables confident expansion. Tier friction can suppress innovation.
Infrastructure decisions should not create psychological hesitation about growth.
6. Ecosystem Alignment: Clarify Strategic Philosophy
Every platform operates within an ecosystem philosophy.
Some centralize credentials within proprietary networks. Others align with open interoperability and decentralized verification.
Ask whether credentials function independently of the vendor’s platform. Can they be validated outside proprietary dashboards? Does the vendor actively support open standards development?
Closed ecosystems can provide cohesive experiences. Open-aligned systems reduce long-term lock-in.
Neither approach is universally correct. The decision should align with your institutional strategy.
If long-term flexibility is a priority, ecosystem independence deserves emphasis.
7. Vendor Stability and Roadmap
Digital credentials become long-lived assets.
Before committing, examine vendor maturity. How long has the product been active? Who are their largest clients? Is their roadmap transparent? Do they participate in standards bodies or industry collaborations?
Request clarity about contingency planning. If the vendor sunsets a product line, what happens to issued credentials?
Migration is always possible. It is rarely simple.
When credentials influence workforce mobility, accreditation, or compliance, vendor stability becomes part of risk management.
8. Credential Lifecycle Governance
Issuance is only the beginning of the credential lifecycle.
Ask how the system handles expiration, revocation, renewal, and version updates. Can credentials be revoked publicly if necessary? Is revocation traceable? Are renewal workflows automated?
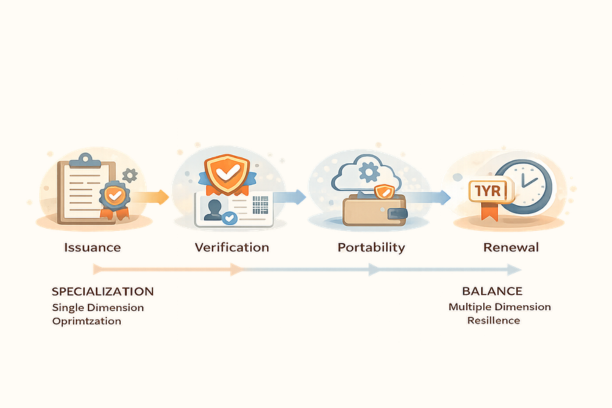 Without lifecycle governance, credentials remain static records. With lifecycle management, they become durable digital assets tied to evolving standards and competencies.
Without lifecycle governance, credentials remain static records. With lifecycle management, they become durable digital assets tied to evolving standards and competencies.
Strong credential lifecycle management ensures that digital proof remains current, defensible, and auditable. We also have a fully informed deep dive on Credential Lifecycle Management, from our blog series for further reading.
These structural shifts explain why evaluation criteria in 2026 look different from even a year ago.
How to Use This Checklist in Practice
During vendor demonstrations, ask these questions directly.
Observe response clarity. Vendors with strong structural foundations typically answer infrastructure questions without deflection. Vendors relying heavily on surface-level differentiation often redirect toward interface polish or marketing positioning.
Documentation matters. Where possible, request written confirmation of standards compliance, export formats, and automation capabilities.
Comparing digital credential management tools requires disciplined evaluation. Feature lists can obscure structural limitations. Infrastructure questions expose them.
Let’s get into it right away, starting with the top 3 in our curated list of Digital credential management platforms.
1. Credly
Credly is one of the most recognized names in the digital credential management space. Its visibility in enterprise certification ecosystems gives it a distinct advantage in environments where employer recognition matters.
 Positioning and Strengths
Positioning and Strengths
Credly performs strongly in workforce-aligned credential programs. Its infrastructure supports high-volume issuance, structured skills mapping, and detailed workforce analytics.
In enterprise settings, employer familiarity with the Credly verification interface can reduce friction during hiring validation. In large corporate ecosystems, standardized verification flows increase perceived legitimacy.
Automation depth is mature. Bulk issuance, structured credential management, and integration capabilities align well with large-scale certification programs.
For organizations prioritizing employer-facing credibility and workforce analytics, Credly remains a leading option.
Structural Considerations
Credly operates within a defined ecosystem model. Credentials are typically tied closely to its network infrastructure. For some institutions, that cohesion is beneficial. For others, it raises portability and dependency considerations.
Pricing architecture is generally aligned with enterprise budgets. Smaller academies or early-stage programs may encounter tier thresholds as volume increases.
Credly is well suited to structured, enterprise-oriented environments. Institutions seeking maximum independence or flexible scaling economics should evaluate ecosystem alignment carefully.
2. Accredible
Accredible has built its reputation around issuance efficiency and operational clarity. It is commonly adopted by training providers, professional certification bodies, and mid-sized institutions transitioning from static certificates to verifiable digital credentials.

Positioning and Strengths
Accredible offers strong automation for bulk issuance and dynamic metadata fields. LMS-triggered credential issuance is well supported, and branded certificate design capabilities are robust.
Its verification flows are generally clean and accessible. Reporting functionality supports compliance and documentation needs in structured learning environments.
For organizations seeking professional-grade credential automation without building infrastructure internally, Accredible provides a streamlined pathway.
Structural Considerations
As with many mature SaaS platforms, feature access often scales with pricing tiers. Institutions expecting rapid growth should evaluate which automation and integration capabilities are included at their projected volume.
Portability discussions may not surface immediately during deployment but can become relevant as credential ecosystems expand.
Accredible performs well when operational efficiency and issuance clarity are central priorities. Long-term ecosystem flexibility should be assessed relative to institutional roadmap.
3. Hyperstack
Hyperstack is a blockchain-native credential management platform built for organizations that need to issue, verify, and manage credentials at scale; without the tier friction or ecosystem lock-in that characterizes larger enterprise platforms.
Positioning and Strengths
Where Credly leads with employer network recognition and Accredible leads with operational simplicity, Hyperstack's differentiator is structural balance: deep automation, open standards alignment, and enterprise-grade security available from the entry tier.
Key capabilities that sets us apart:
- Bulk issuance at genuine scale - Customers report issuing 20,000+ credentials in under 10 minutes. This is not a marketing claim but a documented customer outcome (Niti Aayog, rated on G2). Credly and Accredible support bulk issuance, but Hyperstack's architecture is built around high-volume as a default, not an enterprise add-on.
- Multi-blockchain verification - Hyperstack uses Hedera Hashgraph for credential anchoring, providing tamper-proof, intermediary-free verification. Credentials remain independently verifiable without requiring platform login or active subscription. This is a meaningful structural distinction from hosted verification models.
- Open standards compliance - Hyperstack adheres to Open Badges 2.0 with Open Badge 3.0 alignment in its roadmap. Credentials are portable and wallet-compatible, reducing long-term vendor dependency risk.
- SOC 2 Type 2, EU GDPR, and UK GDPR certified - Enterprise-grade security compliance is included, not reserved for premium tiers. Regular penetration testing and end-to-end data encryption are standard.
- 2,000+ LMS and platform integrations - Native connections to Moodle, Canvas, Blackboard, Docebo, Thinkific, Kajabi, Zoom, Google Forms, and HubSpot. LMS-triggered automated issuance is available without custom development.
- Canva integration + built-in design studio - Credential design is handled in-platform with a full design studio, or via Canva for teams with existing design workflows. No external design tools required.
- Transparent, growth-friendly pricing - A free tier is available for teams getting started. Pricing does not gate core automation or verification features behind enterprise plans, which reduces hesitation around program expansion.
Hyperstack is rated as the best and most user-friendly credential management platform on G2 Crowd, with a 4.8/5 rating from verified users including organizations at Stanford Medicine, Dell, and Santa Clara University.
Structural Considerations
Hyperstack's strength is infrastructure durability rather than network effect. For organizations building credential programs designed to scale, migrate, and remain verifiable over a multi-year horizon, Hyperstack's architecture reduces long-term operational risk.
Best fit for: Training providers, professional certification bodies, higher education programs, and corporate learning teams that need high-volume issuance, open standards portability, and predictable scaling economics without enterprise-tier gating.
Portability alignment and open standards considerations appear integrated into the system’s structural model. This reduces long-term migration friction and ecosystem dependency risk.
Parchment
Parchment is deeply embedded in formal academic record infrastructure, particularly within U.S. higher education ecosystems. Its core competency is official transcript and diploma distribution at an institutional scale.

Positioning and Strengths
Parchment’s strength lies in registrar-grade workflows. It supports:
- Secure transcript exchange
- Official diploma distribution
- Institutional record compliance
- Regulatory-aligned documentation processes
For universities whose primary objective is official academic document transfer between institutions, licensing boards, and regulatory authorities, Parchment provides procedural stability and long-standing institutional familiarity.
Its advantage is not speed or modular flexibility. It is formal authority.
Parchment is widely recognized in traditional academic pipelines, which reduces friction when exchanging official documents within structured ecosystems.
Structural Context
It is important to understand that Parchment has expanded its international academic validation footprint through acquisition, including Digitary. This positions Parchment as a broader academic credential infrastructure provider rather than a purely domestic transcript exchange service.
However, the underlying architectural orientation remains document-centric.
Structural Considerations
Modern digital credentialing increasingly includes:
- Stackable micro-credentials
- Workforce-aligned certifications
- Continuing education credentials
- Modular skill-based programs
Systems originally designed for static document exchange may not naturally support high-frequency, automated, modular credential issuance without additional tooling or workflow adaptation.
Institutions expanding beyond transcript distribution into dynamic credential ecosystems should evaluate whether document-first architecture aligns with credential lifecycle management needs such as automation, analytics, and portability.
Parchment excels at formal record authority. Its suitability for modular credential infrastructure depends on institutional scope.
5. Digitary [by Parchment]
Digitary operates within academic validation, with a specific emphasis on secure digital diploma verification and cross-border credential authentication.

It now operates under Parchment ownership, extending Parchment’s reach into international academic markets, particularly Europe and global diploma mobility ecosystems.
Positioning and Strengths
Digitary’s strengths are concentrated in:
- Secure digital diploma validation
- Cross-border academic verification
- Identity-aligned credential authentication
- European higher education credential frameworks
Where Parchment is strongly associated with institutional registrar workflows, Digitary has historically been associated with international diploma verification and secure digital validation across national boundaries.
Security and authenticity are central to its positioning.
Structural Differentiation
The distinction is subtle but important.
Parchment is registrar workflow infrastructure.
Digitary is validation-layer infrastructure.
Both are rooted in formal academic documentation rather than modular credential ecosystems.
Structural Considerations
As universities expand into workforce-aligned micro-credentials and stackable digital programs, requirements increasingly include:
- Automated issuance pipelines
- Interoperable credential standards
- Lifecycle tracking
- Wallet compatibility
- Dynamic metadata management
Platforms optimized for diploma validation may require supplementary infrastructure when supporting large-scale modular credential issuance programs.
The key distinction institutions must evaluate is whether their primary need is:
- Formal document authority,
- Adaptable credential lifecycle management
Security alone does not define infrastructure completeness.
6. Badgr
Badgr emerged from the open badge movement and has historically aligned itself with Open Badge standards and LMS integrations.

Positioning and Strengths
Badgr’s primary appeal lies in its alignment with open standards. Institutions committed to Open Badge compliance and interoperability often view it as philosophically aligned with portability principles.
Its LMS integrations made it accessible for academic departments launching early-stage digital badge programs. For institutions experimenting with micro-credentials inside structured learning environments, this integration reduces implementation friction.
Portability orientation and standards awareness remain its defining strengths.
Structural Considerations
Open alignment alone does not guarantee operational depth.
As credential programs scale across departments or institutions, orchestration complexity increases. Automation maturity, advanced analytics, and lifecycle governance become more central.
Open ecosystems distribute flexibility. Distributed flexibility requires coordination capacity.
Institutions with strong internal technical oversight may manage this comfortably. Others may encounter operational overhead as scale increases.
Badgr aligns strongly with open badge ecosystems. Buyers planning high-volume, multi-program credential strategies should evaluate automation and lifecycle management depth carefully.
7. Open Badge Factory
Open Badge Factory positions itself squarely within standards-based credentialing ecosystems, particularly in collaborative and consortium-driven environments.

Positioning and Strengths
Its strength lies in structured badge issuance aligned with Open Badge specifications. Institutions participating in multi-institution recognition programs often value this alignment.
Multi-language support and governance tools make it suitable for international or cross-organizational badge ecosystems.
For standards-driven environments prioritizing interoperability and transparency, this orientation is coherent.
Structural Considerations
As credential programs evolve beyond badges into broader digital credential management systems, additional requirements surface.
Workforce analytics, credential lifecycle management, and high-volume automation extend beyond badge issuance itself.
Badge-first platforms perform well within defined ecosystems. When credentials begin interfacing with enterprise hiring systems or compliance frameworks, operational depth becomes more relevant.
Standards compliance is foundational. Infrastructure maturity determines long-term scalability.
8. Sertifier
Sertifier is often adopted by training providers, bootcamps, and organizations running recurring short-form programs.

Positioning and Strengths
Its primary value lies in rapid deployment and straightforward credential issuance. Bulk credential distribution, clean verification links, and operational simplicity make it accessible for teams without dedicated technical infrastructure.
For webinar series, corporate workshops, or online academies scaling moderately, this approach is efficient.
Automation is present in practical forms, particularly for recurring issuance workflows.
Structural Considerations
As credential ecosystems mature, demands extend beyond tactical issuance.
Institutions expanding into workforce-aligned certifications or regulatory-facing programs may require deeper automation logic, broader analytics capabilities, and stronger standards alignment.
Sertifier performs reliably within mid-scale issuance environments. Buyers expecting aggressive multi-year scaling should test integration boundaries and lifecycle features carefully.
Its optimization appears centered on operational efficiency rather than long-term credential infrastructure governance.
9. Certifier
Certifier occupies a similar mid-market space, appealing to organizations transitioning from static PDF certificates to verifiable digital formats.

Positioning and Strengths
Certifier emphasizes ease of use. Bulk uploads, QR-based verification, and customizable certificate templates make onboarding straightforward.
For small-to-mid-sized academies, marketing-driven programs, or organizations focused on quick implementation, this simplicity is valuable.
Issuance workflows are intuitive, reducing operational overhead for non-technical teams.
Structural Considerations
When credentials begin functioning as formal proof in hiring, compliance, or accreditation contexts, infrastructure evaluation becomes stricter.
Portability, lifecycle management, and automation depth may require closer scrutiny in larger-scale deployments.
Certifier performs well in environments where speed and usability are primary. Organizations planning complex credential ecosystems should evaluate extensibility carefully.
Usability and infrastructure durability are not identical dimensions.
10. Give My Certificate
Give My Certificate focuses heavily on event-driven and short-cycle credential programs.

Positioning and Strengths
Its strength lies in automation for high-frequency issuance. Conferences, webinars, and training events benefit from simplified credential delivery workflows.
Email-triggered issuance and shareable verification links support rapid deployment without complex setup.
For organizations issuing credentials tied to recurring events rather than long-term certification tracks, this model is efficient.
Structural Considerations
Event-oriented systems are optimized for velocity. Long-term credential lifecycle management introduces additional requirements.
As volume grows or credentials begin interfacing with workforce systems, expectations around standards compliance, analytics maturity, and integration flexibility increase.
Give My Certificate aligns well with short-cycle programs. Organizations transitioning toward structured, multi-level certification ecosystems may require broader capability sets.
11. Badgecraft
Badgecraft positions itself within experiential and skills recognition ecosystems, often aligning with informal learning and learner-owned credential models.

Positioning and Strengths
Badgecraft emphasizes wallet-based credential storage and recognition of experiential learning. It supports badge ecosystems where community validation and informal skill acknowledgment play central roles.
For youth programs, community education initiatives, and experiential learning environments, this philosophy aligns well. It supports distributed recognition models rather than centralized institutional control.
Standards alignment and learner ownership are meaningful strengths in these contexts.
Structural Considerations
When credentials intersect with enterprise hiring systems, regulatory oversight, or formal certification pathways, expectations shift.
Enterprise-scale automation, advanced analytics, and audit-grade lifecycle management may require additional evaluation.
Badgecraft is optimized for recognition-first ecosystems. Organizations building compliance-sensitive or workforce-integrated credential programs should assess whether infrastructure depth matches those requirements.
Recognition systems and credential infrastructure systems overlap, but they are not identical.
12. BadgeList
BadgeList often appears in internal recognition or small-scale credential deployments.

Positioning and Strengths
Its appeal lies in simplicity. Organizations can create badges quickly and implement recognition programs without significant technical overhead.
Internal team recognition, morale initiatives, and lightweight learning programs benefit from this model.
Administrative complexity is minimal, making it accessible for smaller teams.
Structural Considerations
As credentials move beyond internal recognition into external proof, expectations change.
Employer-facing verification, standards compliance, lifecycle governance, and interoperability requirements extend beyond lightweight recognition workflows.
BadgeList functions effectively in small, contained environments. High-stakes credentialing programs generally require more comprehensive infrastructure.
Scope clarity is essential before adoption.
13. Blockcerts (Framework)
Blockcerts differs from most platforms in this list. It is a technical framework rather than a turnkey SaaS credential management system.

Positioning and Strengths
Blockcerts introduced blockchain-anchored credential verification models. Its emphasis is cryptographic integrity and decentralized proof.
For institutions prioritizing immutability and tamper resistance above all else, this approach is compelling.
Cryptographic anchoring addresses fraud concerns directly and supports independent verification logic.
Structural Considerations
Frameworks require orchestration.
Issuance workflows, automation pipelines, analytics, lifecycle management, and user interfaces must be built or layered on top of the framework.
Institutions adopting blockchain-first models often underestimate operational complexity.
Security addresses authenticity. It does not automatically provide automation maturity, analytics clarity, or scalable governance.
Blockcerts excels at constructing a trust layer. Operational layer management remains a separate consideration.
14. Moodle + Open Badge Plugins
Many institutions rely on LMS-native badge plugins, particularly within Moodle ecosystems.

Positioning and Strengths
When credentialing needs remain tightly coupled to course completion inside an LMS, native badge plugins offer efficiency.
Issuance is integrated into existing workflows. Administrative familiarity reduces onboarding time. Incremental cost may be lower compared to standalone systems.
For internal learning recognition programs, this integration can be sufficient.
Structural Considerations
An LMS is designed for learning delivery. A digital credential management system is designed for long-term proof infrastructure.
When credentials must function beyond the LMS, portability, external verification perception, and lifecycle governance complexity increase.
Institutions planning cross-platform credential ecosystems often outgrow LMS-native solutions.
Integration convenience should not obscure long-term infrastructure limitations.
Emerging Vendors
The digital credential management landscape continues evolving.
New vendors regularly enter the market, emphasizing AI-assisted verification, advanced skills graph mapping, deeper blockchain anchoring, or workforce alignment integrations.
Positioning and Strengths
Emerging vendors often innovate rapidly. They may offer modern interfaces, novel analytics perspectives, or experimental credential interoperability models.
Early adopters can gain competitive differentiation through innovation.
Structural Considerations
Infrastructure decisions require durability.
Emerging platforms should be evaluated against several risk indicators:
- Standards compliance maturity
- Vendor longevity and funding stability
- Data portability guarantees
- Roadmap transparency
- Migration contingency planning
Innovation and durability must coexist.
Novel features can create advantage. Unproven stability can create migration risk.
In infrastructure planning, long-term resilience generally outweighs short-term novelty.
Comparison Table
The following matrix is a structural snapshot.
Each platform is positioned according to its dominant architectural orientation across verification integrity, portability, automation depth, analytics maturity, ecosystem flexibility, and scaling predictability.
The goal is not to declare a universal winner but to reveal where each system concentrates strength and where tradeoffs may emerge as programs expand.
Viewed this way, the table becomes less about feature parity and more about infrastructure assessment.
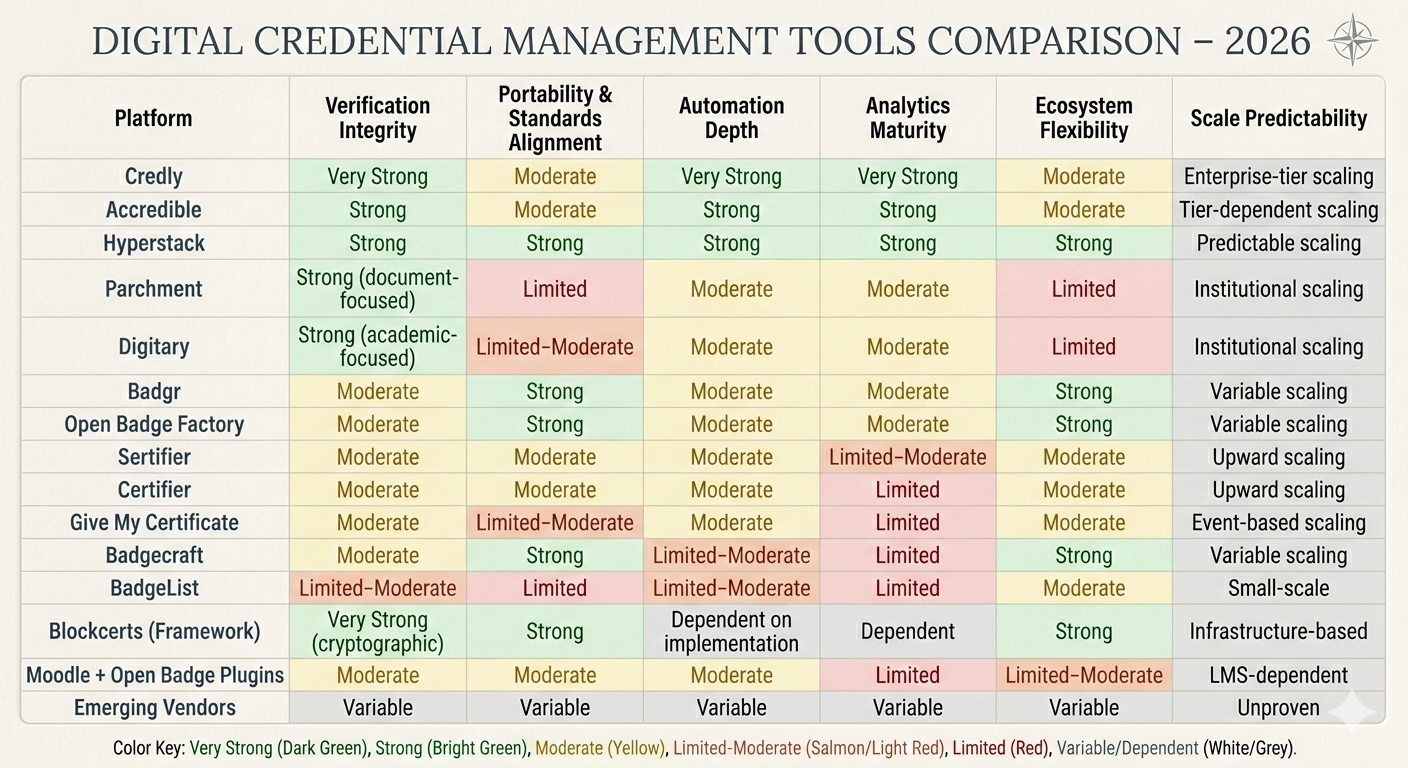 A feature comparison of our top 14 digital credential management systems.
A feature comparison of our top 14 digital credential management systems.
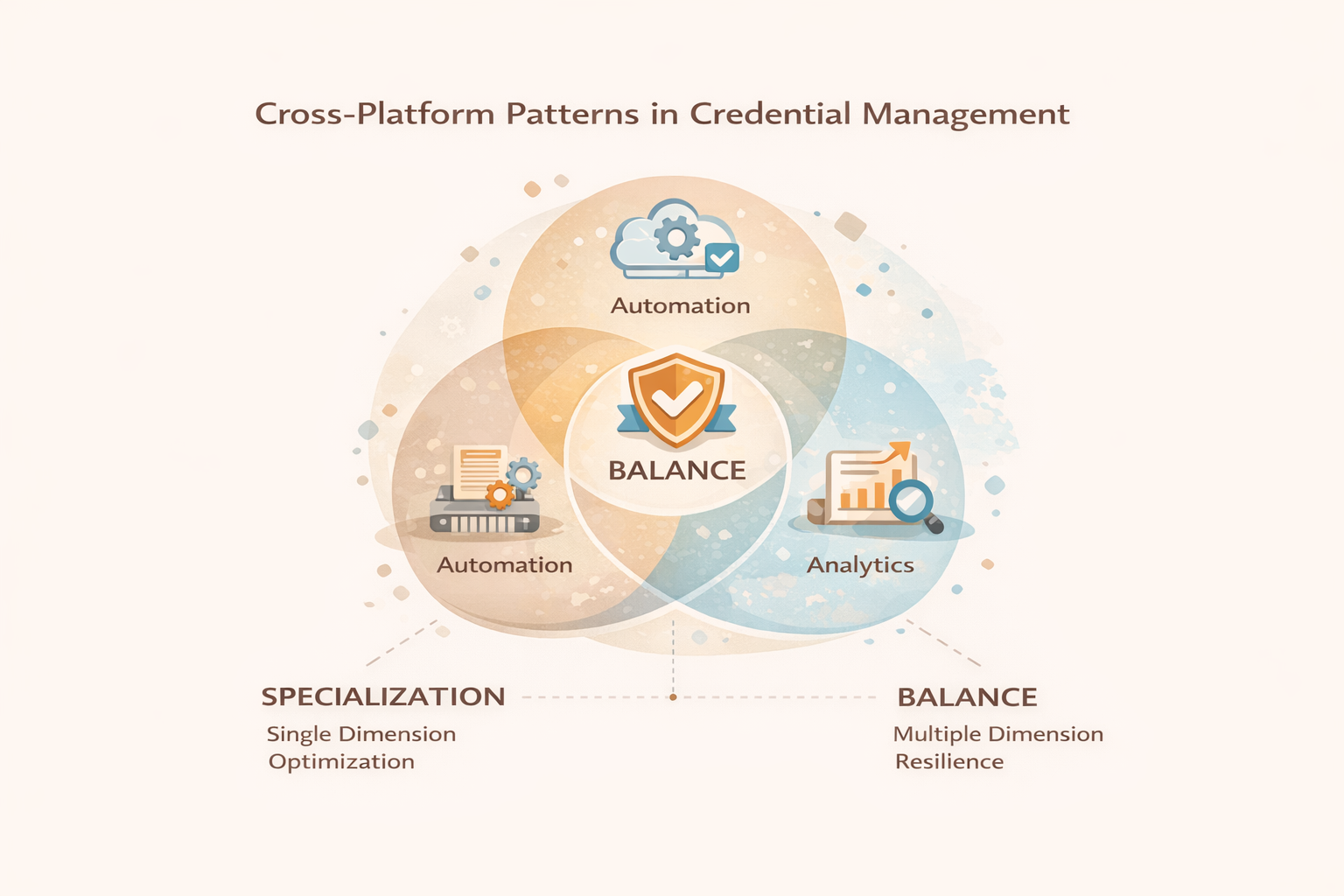
After reviewing 14 digital credential management tools, several structural patterns become visible.
First, no platform dominates across every evaluation dimension. Most tools are optimized around a core philosophy.
Enterprise-oriented platforms tend to excel in analytics maturity and automation depth. Their systems are designed for structured workforce programs and large-scale certification pipelines. However, they may introduce pricing tier thresholds or deeper ecosystem dependency.
Academic record systems prioritize document authority and institutional process alignment. Their strength lies in transcript-level credibility and regulatory familiarity. When credential programs extend into modular or workforce-integrated ecosystems, agility becomes a separate consideration.
Open standards-aligned platforms emphasize portability and interoperability. They reduce vendor dependency risk but vary in automation depth and lifecycle orchestration.
Event-driven and mid-market tools prioritize operational efficiency. They support rapid issuance and practical workflows but may require further evaluation as programs mature into infrastructure-scale deployments.
Blockchain-first frameworks prioritize integrity at the trust layer. They require operational systems layered above them to handle lifecycle management and automation maturity.
Across categories, the most consistent tradeoff appears between specialization and balance.
Specialized systems excel in one dimension. Balanced systems avoid structural weaknesses across multiple dimensions.
This pattern becomes clearer at scale.
Structural Synthesis: What Separates Balanced Systems
When credential programs remain small, specialization often suffices.
When programs expand across departments, geographies, or workforce ecosystems, structural coherence becomes more important.
Balanced credential management systems tend to demonstrate:
- Verification models that remain durable beyond subscription cycles
- Portability aligned with open standards
- Automation depth without restrictive tier gating
- Analytics capable of informing strategic decisions
- Predictable scaling economics
Specialized platforms may dominate in workforce analytics, transcript exchange, or event automation. Balanced platforms reduce long-term migration and dependency risk.
The difference often does not surface during onboarding.
It appears during expansion, integration with external systems, or regulatory scrutiny.
Credential infrastructure maturity is defined not only by what it enables today, but by what it prevents from breaking tomorrow.
Systems designed with lifecycle governance in mind generally adapt more easily to evolving requirements.
Closing Strategic Guidance
Choosing among digital credential management tools should begin with strategic clarity rather than vendor comparison.
Define your primary objective first.
If your goal is formal transcript exchange, document-focused systems may align naturally.
If your goal is enterprise workforce certification tied to employer recognition, network familiarity and analytics maturity may carry more weight.
If your objective is building a portable, standards-aligned credential ecosystem designed to evolve over several years, structural balance becomes more important than dominance in any single category.
Project three scenarios before deciding:
- Your credential volume doubles
- You migrate learning platforms
- You expand into new regulatory or workforce markets
Evaluate which system adapts with minimal friction.
Digital credentials increasingly function as proof infrastructure, not decorative artifacts.
Infrastructure decisions should prioritize durability, portability, and operational coherence over short-term convenience.
The strongest digital credential management tools are those that continue functioning predictably when scale, regulation, and ecosystem complexity increase.
That is the lens through which 2026 decisions should be made.
Not sure which system is right for you?
Every credential program is different. Book a quick conversation with our team to discuss your specific needs, use case, and scale requirements. We'll help you cut through the noise, at your convenience.
Schedule Your Conversation
Sources and References
Standards & Technical Frameworks
- W3C Verifiable Credentials Data Model
- Open Badges 3.0 Specification
- IMS Global Learning Consortium documentation
Workforce & Skills Research
- World Economic Forum – Future of Jobs Report
- LinkedIn Workplace Learning Report
- OECD Skills Outlook publications
- Public product documentation and pricing pages of reviewed platforms
- Open standards community forums and GitHub repositories
- Higher education credential exchange case studies
Credential Fraud & Verification Research
- Academic research on digital credential integrity
- Public case studies on transcript fraud and certificate tampering
FAQs
1. What is a digital credential management system?
A digital credential management system is a platform that enables organizations to design, issue, verify, and manage digital certificates and badges at scale. Unlike simple certificate generators, credential management systems include verification mechanisms, automation workflows, portability support, and analytics for tracking credential performance over time.
2. How is a digital credential management system different from a certificate generator?
Certificate generators focus primarily on design and issuance. Credential management systems treat credentials as long-lived digital assets. They typically include tamper-resistant verification, automation via APIs or LMS integrations, standards alignment such as Open Badges, and lifecycle tracking beyond initial issuance.
Key evaluation criteria include:
- Verification integrity and tamper resistance
- Portability and standards alignment
- Automation depth and API availability
- Analytics maturity
- Pricing scalability
- Vendor stability and roadmap transparency
The right choice depends on whether your goal is document exchange, workforce certification, event-based issuance, or long-term infrastructure.
4. Are Open Badges and W3C Verifiable Credentials important in 2026?
Standards such as Open Badge 3.0 and W3C Verifiable Credentials have gained relevance because they support portability and interoperability. Organizations planning long-term credential ecosystems increasingly evaluate whether credentials can function independently of a single vendor platform.
5. Do employers verify digital credentials?
Employers do not verify every credential, but when verification occurs, speed and clarity matter. A verification flow that is immediate and tamper-resistant improves credibility. Systems that require complex login processes or unclear validation paths can reduce trust.
That depends on architecture. Platforms aligned with open standards and export-friendly data structures reduce migration risk. Systems tightly coupled to proprietary ecosystems may require more complex transition planning if infrastructure changes.
7. Are blockchain-based credential systems more secure?
Blockchain anchoring strengthens credential integrity at the trust layer. However, operational features such as automation, analytics, and lifecycle management must still be layered on top. Security alone does not guarantee scalability.